Serious Vulnerability Found in CrushFTP, Cybercriminals Have Begun Exploiting It!
Active Exploitation of CVE-2025-2825 Vulnerability! 🔴
After the discovery of an authentication bypass vulnerability in CrushFTP, cybercriminals have started actively exploiting it. According to data from the Shadowserver Foundation, as of March 30, 2025, 1,512 vulnerable servers remain exposed to the internet. The majority of these vulnerable servers are located in North America (891 servers).
This issue affects CrushFTP versions 10.0.0 – 10.8.3 and 11.0.0 – 11.3.0. The CVE-2025-2825 vulnerability is rated 9.8 on the CVSS scale and, if exploited, can lead to complete server compromise.
Experts note that the vulnerability arises due to an error in the S3 protocol authentication process. The attack is carried out in three steps:
1️⃣ Spoofing the AWS header — using the “crushadmin” username to deceive the server.
2️⃣ Creating a fake cookie — forging the CrushAuth value, which is 44 characters long, to bypass authentication.
3️⃣ Manipulating the c2f parameter — bypassing password checks.
As a result, an attacker gains unauthorized access to the server without needing to authenticate!
Shadowserver’s monitoring data shows the following distribution of vulnerable servers:
🌎 North America: 891 servers
🌍 Europe: 490 servers
🌏 Asia: 62 servers
🌍 Oceania: 45 servers
🌍 South America and Africa: 12 servers each
These figures show that thousands of systems are at risk globally.
CrushFTP has released versions 11.3.1 and 10.8.4 that fix this vulnerability. The updates include the following security measures:
✅ Strengthening S3 authentication security.
✅ Adding the parameter s3_auth_lookup_password_supported=false.
✅ Implementing correct authentication flow checks.
💡 To ensure security, take the following actions:
🔹 Immediately update to CrushFTP version 11.3.1 or 10.8.4!
🔹 If immediate updating is not possible, enable the DMZ feature as a temporary protection measure.
🔹 Check server logs, especially for GET requests to the URL /WebInterface/function/.
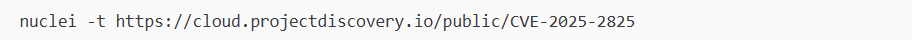
🔹 Use the free scanning tool:
CrushFTP has previously encountered serious vulnerabilities, such as CVE-2023-43177, which allowed attackers to gain unauthorized access to files and execute arbitrary code. These vulnerabilities serve as entry points for attackers to infiltrate corporate networks.
📢 The CVE-2025-2825 vulnerability is a serious threat and is actively being exploited by cybercriminals.
⚠️ If you are using CrushFTP, do not delay updating!
🚀 Install the update and strengthen your server’s security!
This vulnerability is simple to exploit, so ensure your servers are not targeted by cybercriminals! 🔐