Serious Threat to Apple Devices: Three New Zero-Day Vulnerabilities Are Being Actively Exploited!
Apple has announced the discovery of three new zero-day vulnerabilities that are currently being actively exploited by cybercriminals. These vulnerabilities, identified as CVE-2025-24200, CVE-2025-24201, and CVE-2025-24085, pose a significant threat to iPhones, iPads, Macs, and other Apple ecosystem devices.
Hackers can exploit these vulnerabilities to gain physical access to a device or execute attacks via malicious web content. As a result, Apple strongly advises all users to update their devices immediately and take additional security precautions.
Details of the Vulnerabilities
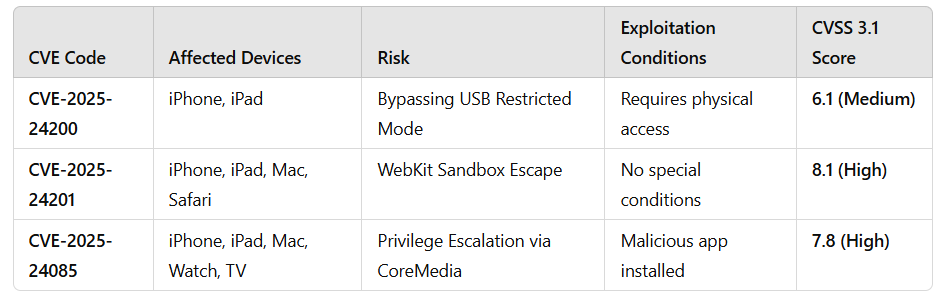
1. CVE-2025-24200 – Bypassing USB Restricted Mode
✅ Affected devices: iPhone, iPad (iOS 18.3.1, iPadOS 18.3.1, iPadOS 17.7.5)
✅ Risk: Attackers can disable USB Restricted Mode even when the device is locked.
✅ Exploitation conditions: Requires physical access to the device.
✅ Potential impact: Enables unauthorized access using forensic analysis tools or hacking techniques.
➡️ Note: Apple states that this vulnerability “has been used in highly sophisticated attacks targeting specific individuals.” It was discovered by Bill Marczak from The Citizen Lab (Munk School, University of Toronto).
2. CVE-2025-24201 – WebKit Sandbox Escape
✅ Affected devices: iOS, iPadOS, macOS Sequoia, visionOS, Safari
✅ Risk: Attackers can bypass WebKit’s sandbox restrictions, allowing them to evade security protections.
✅ Exploitation conditions: No special access is required – can be executed over the internet.
✅ Potential impact: Users may be compromised by malicious code embedded in harmful web pages.
➡️ Note: This vulnerability was introduced as an additional fix to block attacks in iOS 17.2. However, devices running versions older than iOS 17.2 remain vulnerable.
3. CVE-2025-24085 – Privilege Escalation via CoreMedia
✅ Affected devices: iOS, iPadOS, macOS, watchOS, tvOS, visionOS
✅ Risk: A use-after-free (UAF) vulnerability in CoreMedia allows attackers to escalate privileges.
✅ Exploitation conditions: Requires a malicious app to be installed on the device.
✅ Potential impact: The attacker can gain administrator-level privileges and take full control of the device.
➡️ Note: Apple has confirmed that this vulnerability has been actively exploited in attacks on devices running iOS versions older than 17.2.
Vulnerability Overview
How to Protect Yourself?
Apple has already released security updates to address these vulnerabilities:
🔹 iPhone & iPad: Update to iOS 18.3 / iPadOS 18.3.
🔹 Mac: Install macOS Sequoia 15.3.
🔹 Apple Watch: Update to watchOS 11.3.
🔹 Apple TV: Update to tvOS 18.3.
🔹 Apple Vision Pro: Apply visionOS 2.3 update.
📌 How to Update Your Device:
1️⃣ Go to Settings → General → Software Update.
2️⃣ Enable Automatic Updates to receive security patches as soon as they are available.
Additional Security Recommendations
🔹 Be cautious when installing third-party apps – apps from unverified sources may contain malware.
🔹 Enable Lockdown Mode – this feature reduces attack surfaces within the Apple ecosystem.
🔹 Avoid clicking on suspicious links – attackers may exploit the WebKit vulnerability through malicious websites.
🔹 Regularly back up important data – maintaining backups is a crucial part of any security strategy.
These three zero-day vulnerabilities pose a severe risk to Apple users. The ability to bypass USB Restricted Mode, break through WebKit security barriers, and escalate privileges via CoreMedia creates significant opportunities for attackers.
Although Apple has promptly released patches, users must update their devices immediately! Otherwise, these vulnerabilities could continue to be exploited by cybercriminals.
📢 Ensure your security – update your Apple device now! 🚀